2018湘湖杯逆向题
首先先查看文件
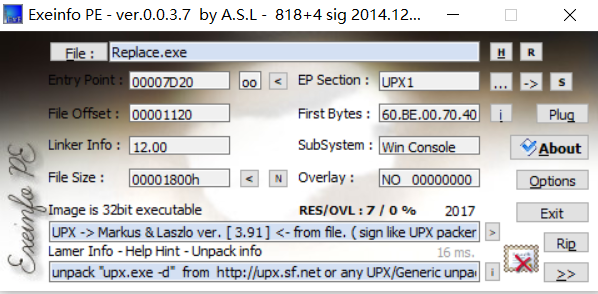
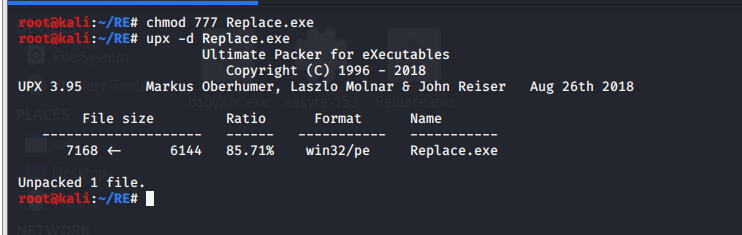
upx壳,32位文件,于是拖入kali下手动脱壳。
把已经脱壳的文件拖入ida中查看,反编译
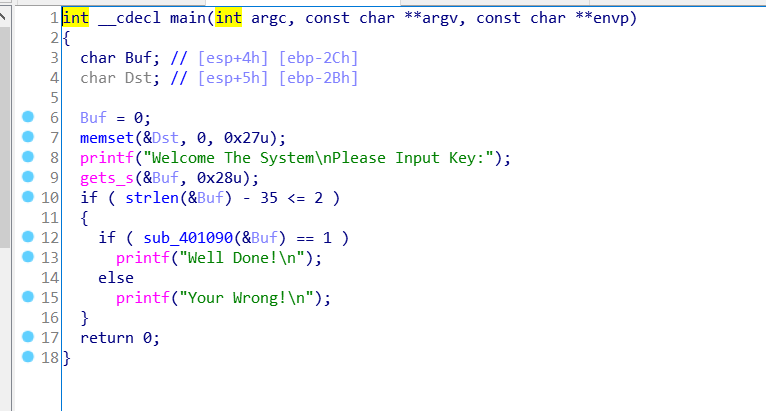
里面有个重点输入buf必须是35长度
进入sub_401090函数看看
signed int __fastcall sub_401090(int a1, int a2) |
需要这个函数返回1 那肯定是要完成
if ( ++v4 >= 35 ) |
那看看上面的函数逻辑 v5 = *(_BYTE *)(v4 + v2);
v2被a1赋值,a1就是我们输入的buf
v4从0开始每次循环+1
接着看一下下面v6 = (v5 >> 4) % 16; v6=(输入的每个字符/16)%16v7 = (16 * v5 >> 4) % 16;
v7= v5%16
v8 = unk_402150[2 * v4];
v8为一个数组中2v4的变量 我们暂且叫这个数组为arr1 v8=arr1[2v4]
if ( v8 < 48 || v8 > 57 ) |
这一段是判断v8去对v9进行操作v10 = byte_402151[2 * v4];v10等于另外一个数组的2v4个元素 我们暂且叫这个数组为arr2 v10 = arr2[2v4]
if ( v10 < 48 || v10 > 57 ) |
下面就是一个重点 这是整个代码的关键所在 在byte_4021A0这个数组中的16v6+v7的位置上的字符 需要和v11+v12对0x19的异或值相等才可以
简洁而写就是byte_4021A0[16*v6+v7] == (v11+v12)^0x19
整理了所有逻辑后我们就去思维逆回去 我们需要有一个字符串 长度必须是35 而且字符串中每一个都在if ( (unsigned __int8)byte_4021A0[16 * v6 + v7] != ((v11 + v12) ^ 0x19) )
可以跳过 那可以想象得到 估计这个就是flag字符串了 那我们怎么得到这个字符串呢 最简单方法 爆破 从所有可见字符一个一个试试 看到哪一个成立就行 先看一下byte_4021A0,byte_402151 和 byte_402150
数组中存的都是什么
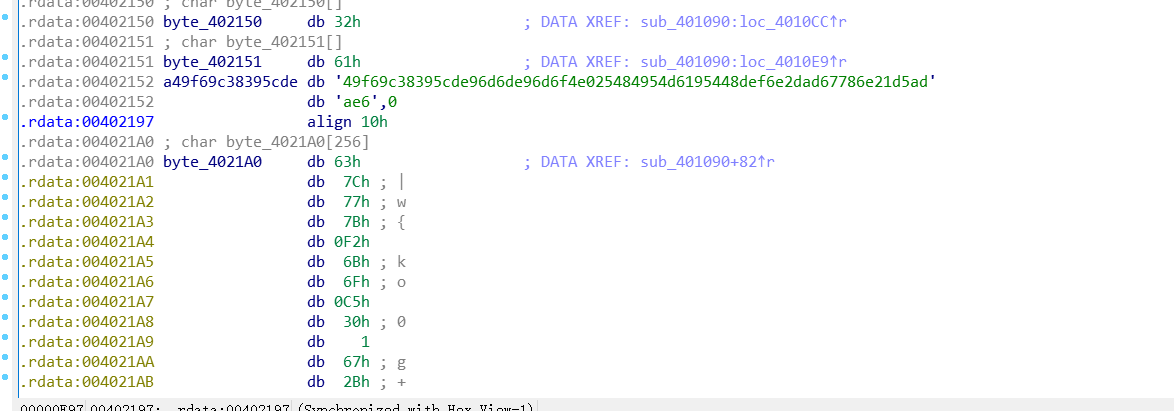
可以看的出来byte_402151 和 byte_402150是连着的 byte_402150存的是2a49f69c38395cde96d6de96d6f4e025484954d6195448def6e2dad67786e21d5adae6
而byte_402151存的是 a49f69c38395cde96d6de96d6f4e025484954d6195448def6e2dad67786e21d5adae6
shift+E提取出byte_4021A0的数据
unsigned char ida_chars[] = |
最后附上脚本
table = [0x63, 0x7C, 0x77, 0x7B, 0xF2, 0x6B, 0x6F, 0xC5, 0x30, 0x01, |
得到flag
flag{Th1s_1s_Simple_Rep1ac3_Enc0d3} |